The Houthi attacks have disrupted global trade and raised concerns of a wider regional conflict amid the Israel-Hamas war. China's public response has been cautious, with calls to end attacks on civilian ships and veiled criticism of US-led military operations against the Houthis.
China, being the world's largest trading nation, faces high stakes as most of its exports to Europe pass through the Red Sea, and significant amounts of oil and minerals transit the waterway to reach Chinese ports. Despite having an anti-piracy task force in the Gulf of Aden, China has not joined the US-led coalition to protect ships in the Red Sea.
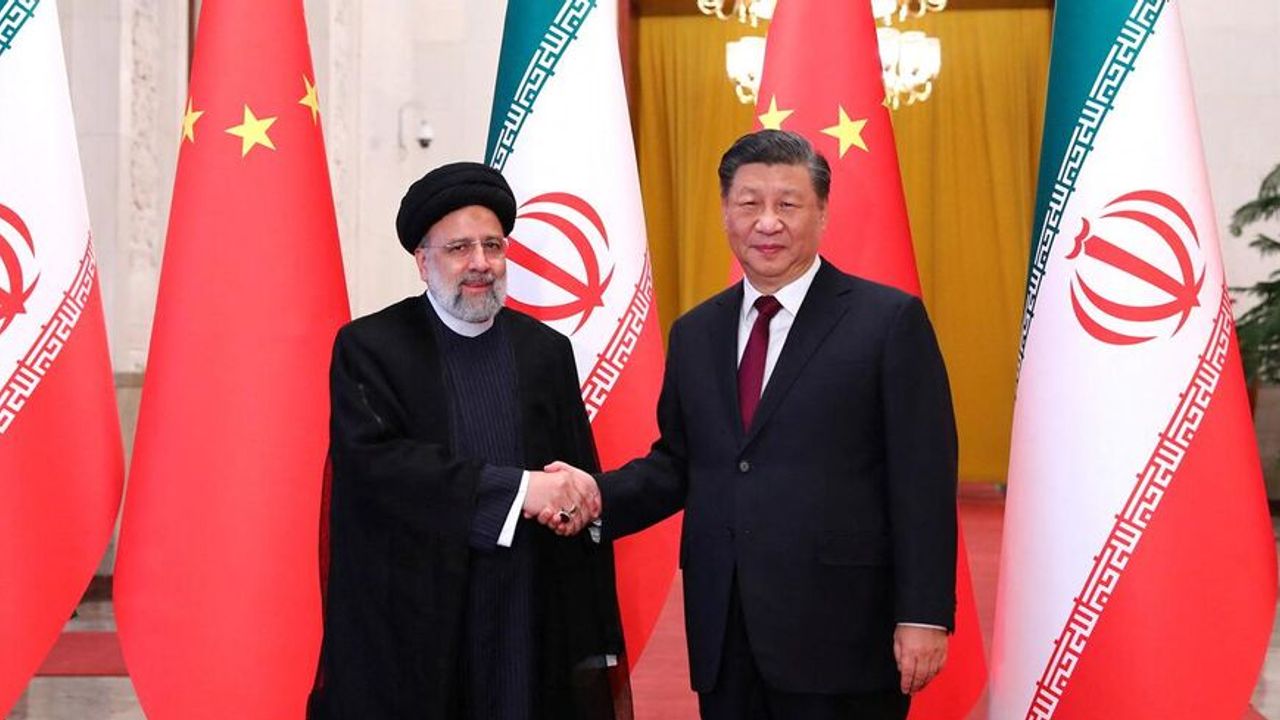
The article highlights the diplomatic challenge for Chinese leader Xi Jinping, who has emphasized contributing "Chinese wisdom" to peace in the Middle East. China's reluctance to directly engage in the Red Sea crisis aligns with its geopolitical calculations, avoiding strengthening the US position in the region.
As the US seeks China's support in pressuring Iran, which supports the Houthis, Chinese officials have urged Iran to rein in the attacks to avoid harming business relations with Beijing. However, China's response is seen as falling short of its global aspirations, raising questions about its role as a diplomatic and security actor in the Middle East.
The article also mentions China's past efforts, such as brokering a Saudi-Iran rapprochement, but notes that its approach in the region is primarily driven by economic interests. China's limited leverage to impact Iran's behavior and uncertainties surrounding its political capital are highlighted.
The escalation of conflict in the Middle East raises questions about the effectiveness of Xi's Global Security Initiative (GSI), which advocates resolving conflicts through development. The article suggests that when faced with actual security threats, such as terrorism and attacks on global shipping, normative approaches may not be sufficient, and hard security solutions are needed.